Nano designs, builds, and manages bespoke, mission-critical integrations between Workforce Management, Project Management, Timesheets, Payroll, HRIS, and ERP systems for complex mid-market and enterprise customers.
Trusted by the HCM x ERP Industry’s Leading Platforms
Predictable Costs. Zero Capacity Surprises.
Eliminate the uncertainty of variable professional services and usage-based billing with fixed price services and subscriptions.
Our Fixed Pricing Formula:
Fixed Price Services
Paid upon completion
Fixed Annual Subscription
Paid annually in advance
- Defined Workflow Integrations: an integration workflow flow is a mapped, dedicated, mission-critical data path.
- Capacity Absorbed: our serverless architecture means we absorb all underlying API transaction volume, server capacity, and usage costs.
- Fixed Professional Services: your bespoke integration build is paid in fixed-price instalments upon completion of milestones.
Our Delivery Process
From discovery to deployment, we follow a rigorous, security-first methodology to ensure your integrations are fit for purpose, robust and scalable.
Scope
Discovery & definition
Design
Architecture & logic
Build
Secure development
Test
QA & validation
Deploy
Go-live execution
Manage
Monitor & support
When Integration Complexity Demands Ongoing Certainty
Bring Nano In When:
- Your client has 100 to 10,000+ employees across multiple apps (Workforce, Projects, Timesheets, Payroll, HRIS, ERP).
- There are complex, multi-step business processes involving multiple business units or geographies.
- The integration is mission-critical e.g. payroll or ERP data integrity, and cannot fail.
- Dynamic & Custom Field Mapping e.g. Maps to your specific enterprise GL codes and unique HRIS fields.
- Event-Driven Guardrails i.e. precise triggers around pay run locks and processing states to prevent data duplication.
- Webhook Native i.e. real-time, event-based updates that ensure system integrity the second a change occurs.
- Traceability i.e. every event logged, timestamped and verified.
Use Standard Connectors When:
- Businesses with simple, single-entity data flow requirements.
- Clients who prefer to staff, build, and support their own integrations internally.
- Integrations that require minimal customisation or unique business logic.
- Static, one-size-fits-all.
- Simple “If this, then that”
-
Standard Polling (Laggy)
- Black Box (Did it work?)
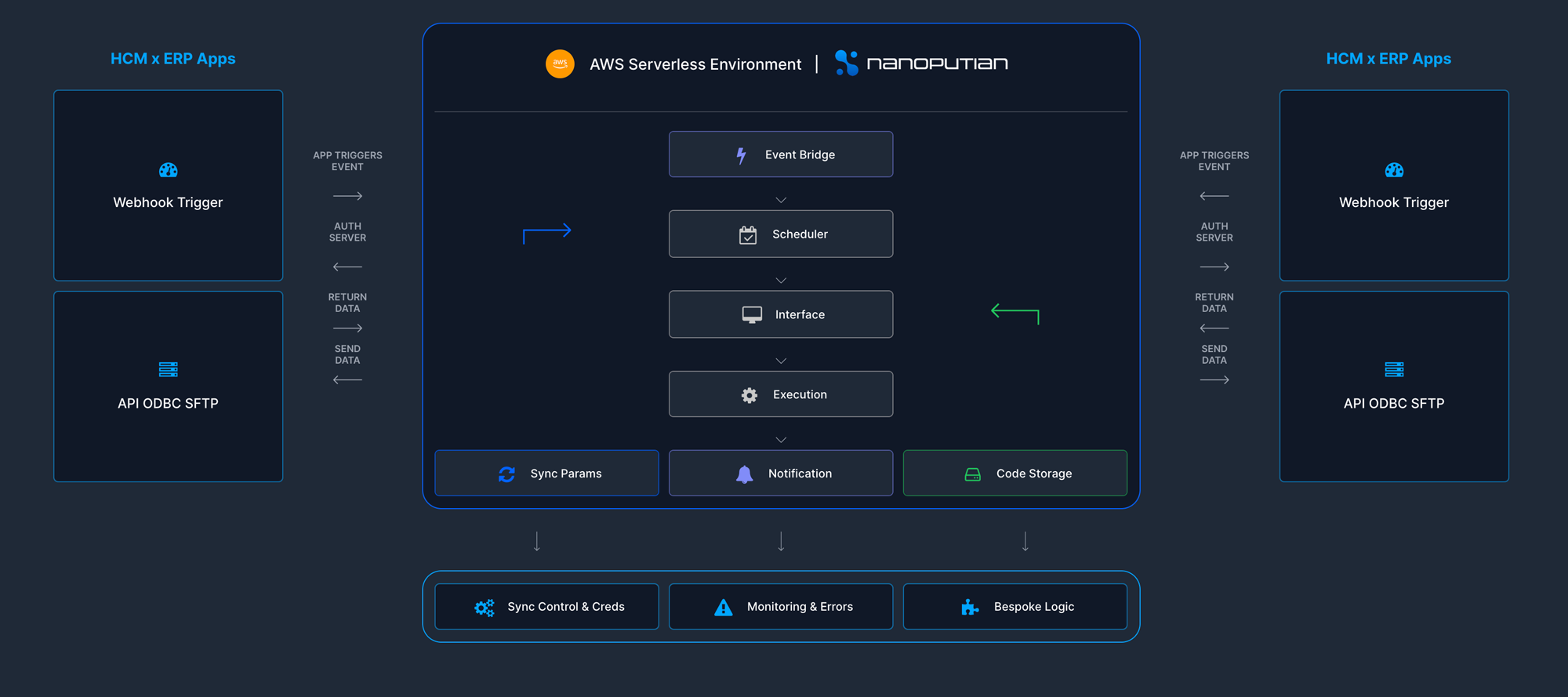
Built for Enterprise Reliability
A secure, serverless event-driven architecture designed to handle high-volume, complex data integrity challenges. Most integrations assume everything will go right. NanoConnect is built for when things go wrong. We don’t just move data; we enforce the business logic e.g. pay run locks, custom field integrity and event-sensitive processing that keeps your Workforce Management, HRIS, Payroll and ERP in perfect sync #GetNanoGetPaid
HCM x ERP Apps
Webhook Trigger
App Triggers
Event
Server
API ODBC SFTP
Data
Data
AWS Serverless Environment |
Event Bridge
Scheduler
Interface
Execution
Sync Params
Notification
Code Storage
HCM x ERP Apps
App Triggers
Event
Server
Webhook Trigger
Data
Data
API ODBC SFTP
Sync Control & Creds
Monitoring & Errors
Bespoke Logic
The Nano Way
Trust
We earn the right to be a trusted & safe integration partner.
Clarity
We make the complex simple, commercially & technologically.
Custom
We enable bespoke
business processes.
Transparency
We share the good, the bad and the ugly. And, we do what we say.
Reliability
Our integrations just work & our humans are obsessed with support.
You can’t run BI or AI on ‘maybe’ data.
Nano Insights is a reusable, trusted data pipeline designed to feed directly into your organisation’s data lake ensuring your data foundations are match fit in an AI-first world.
Why IT, HR & Finance executives choose Nano Insights:
- Trusted Traceability: Nano solves the ‘trust deficit’ in BI and AI. Nano’s event-level logs serve as the Truth Layer for your data lake with out-of-the-box auditability ensuring every transaction is verified before it hits your BI and AI tools.
- Zero-Schema Risk: We support four major platforms OneLake (Fabric), Snowflake, AWS Redshift, and Google BigQuery using a raw JSON approach meaning zero breakage risk when upstream APIs change fields.
- The Translation Layer: Nano bridges the gap between your IT infrastructure and the nuanced business needs of HR, Finance and your Executive team.
The People Behind the Platform

Matt Clarke
General Manager
Matt is Nano’s Head Coach and drives the strategic vision of Nanoputian, bringing his deep partnership expertise and enterprise software ecosystem experience to complex integration delivery.

Jack Stuart
Head of Delivery
Jack is Nano’s Chief Wrangler leading Process Mapping and Project Delivery ensuring integrations are fit for purpose, secure and resilient.
Ready to Offload Your Integration Problem?
If integration friction is slowing down your deal flow or inhibiting your customer’s employee UX, let’s talk. Nano will remove integration friction for your customers with pricing and service certainty.